Account access in Web3 is still defined by a single assumption: users will not lose their keys. In production environments, this assumption does not hold.
Seed phrases act as the root of ownership in most wallets. They also introduce a single point of failure. If lost, access cannot be restored. If exposed, assets can be drained without recourse.
This is not a usability issue. It is a structural limitation in how wallet systems are designed.
As applications move toward embedded onboarding and continuous execution, this limitation becomes more visible. Systems can onboard users in seconds, but they cannot reliably restore access. This creates a gap between onboarding and long-term usability.
Account recovery without a seed phrase is not an enhancement. It is a requirement for systems that need to operate reliably over time.
The Structural Limitation of Seed Phrase-Based Wallets in Crypto Wallet Security
Traditional wallets are built on Externally Owned Accounts, where control is tied directly to a private key represented as a seed phrase.
This model ensures strong ownership guarantees. It also removes any possibility of recovery.
Crypto wallet security in this model is rigid:
- The user holds the key
- The system does not intervene
- Loss of access is permanent
For early users, this tradeoff was acceptable. For production applications, it introduces systemic risk.
Industry analysis suggests that a significant portion of crypto assets is permanently inaccessible due to lost keys. Chainalysis estimates roughly 3.7 million BTC, close to 20 per cent of the circulating supply, is permanently inaccessible due to lost keys.
The constraint sits in the protocol, not the user.
Where Web3 Wallet Infrastructure Breaks
Modern Web3 systems have improved onboarding and execution:
- Embedded wallets remove dependency on browser extensions
- Authentication-based access reduces friction
- Smart accounts enable programmable execution
- Paymasters remove gas constraints
These improvements solve entry and interaction. They do not address loss of access.
When access breaks due to device changes, expired sessions, or compromised credentials, most systems cannot recover state. There is no built-in mechanism to restore continuity.
Current Web3 wallet infrastructure is optimized for:
- Account creation
- Transaction execution
It is not designed for access continuity.
Consider a DeFi protocol with an embedded wallet flow. A user onboards with email in under 30 seconds, deposits into a yield position, then loses access to their device six weeks later. The smart account still holds the position. The paymaster still sponsors gas. The bundler still accepts user operations. None of this matters, because there is no path back to the account. Execution infrastructure works. Access infrastructure does not exist.
This creates a clear operational gap.
Account Recovery Without Seed Phrase: A Shift in Responsibility
Account recovery without a seed phrase changes where responsibility lives.
Instead of relying on users to manage static secrets, systems manage access through controlled mechanisms. Recovery becomes a function of system design rather than user memory.
This introduces a different access model:
- Identity is linked to authentication
- Account control is programmable
- Recovery follows predefined rules
Access is no longer tied to a single artifact. It is maintained through verifiable conditions.
Security guarantees shift from key custody to policy enforcement.
Instead of protecting a single key, systems enforce:
- Authentication validity
- Policy constraints
- Execution rules
The result is controlled recovery without exposing key material.
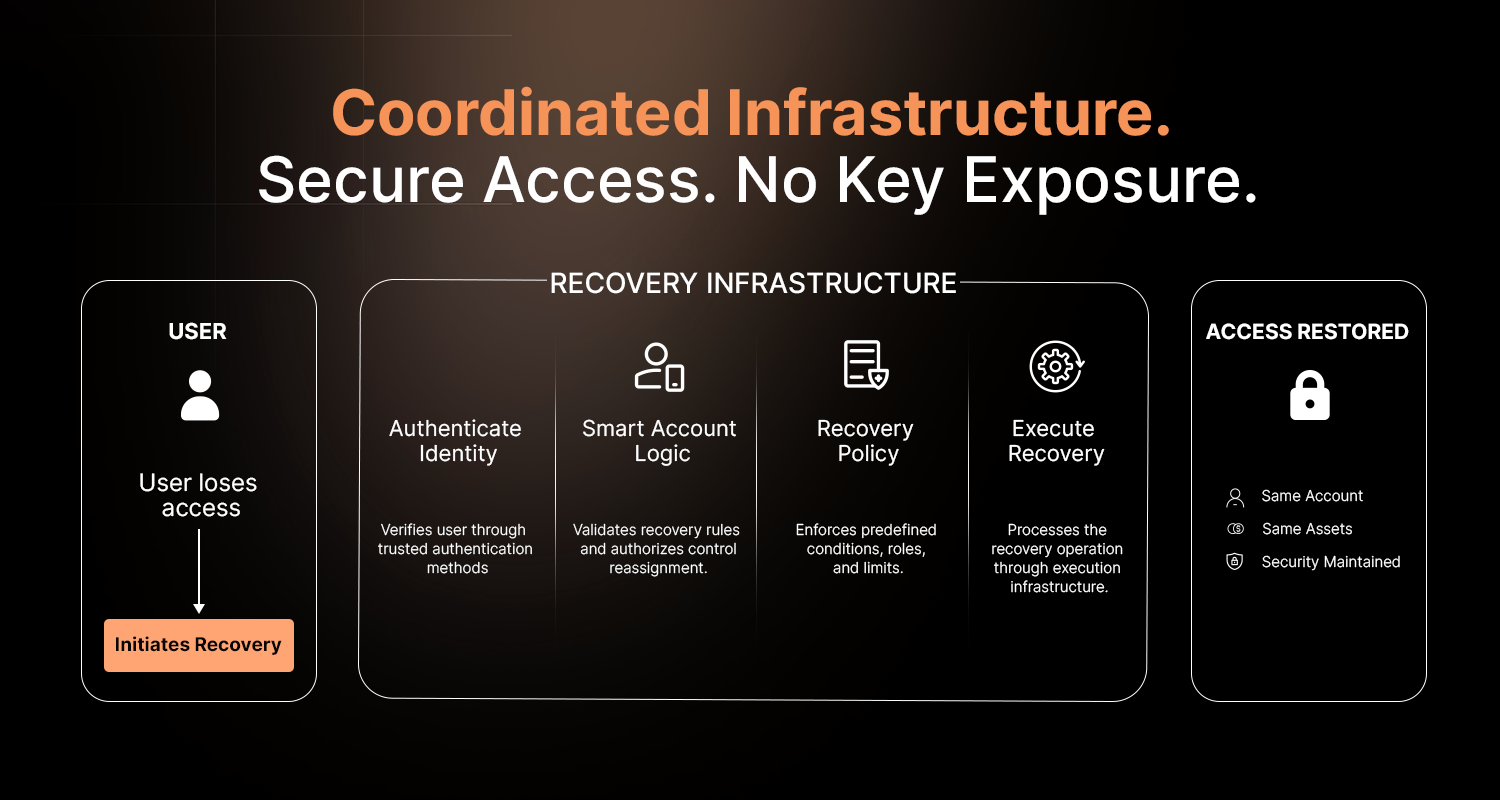
Wallet Recovery Solutions Require System-Level Coordination
Wallet recovery solutions are often treated as isolated capabilities. In practice, recovery depends on coordination across multiple layers.
Authentication layer
Maintains identity continuity through email, passkeys, or social login.
Account layer (smart accounts)
Defines how control can be reassigned or restored.
Policy layer
Enforces conditions such as:
- Who can recover
- Under what circumstances
- Within what limits
Execution layer
Ensures recovery actions are processed reliably.
Without alignment across these layers, recovery becomes inconsistent. Partial implementations introduce more risk than they remove.
Recovery must operate as a unified system.
Smart Accounts Enable Recovery, But Do Not Complete It
Smart accounts introduce programmability at the account level, making recovery logic possible.
They allow:
- Rule-based access control
- Delegated permissions
- Conditional execution
However, they do not solve recovery independently.
Without authentication systems and identity mapping, the account cannot determine who should regain access. Without coordinated infrastructure, recovery cannot execute reliably.
Smart accounts define capability. Systems define reliability.
Web3 Wallet Infrastructure Must Handle Failure by Design
In production systems, failure is expected. Wallet infrastructure must account for it.
Handling failure means:
- Restoring access without exposing private keys
- Maintaining identity continuity across devices
- Enforcing recovery policies deterministically
- Executing recovery actions reliably
Recovery cannot depend on manual intervention or external coordination. It must be embedded into the same system that handles onboarding and execution.
When designed this way:
- Access becomes durable
- System behavior remains predictable
- Operational risk is reduced
Abstraxn’s Approach to Account Recovery Without Seed Phrase
Abstraxn treats recovery as part of wallet infrastructure, not as an external feature.
Embedded wallets establish identity at onboarding through familiar authentication methods. This creates a consistent access layer from the first interaction.
Smart accounts define how control is managed, enabling programmable recovery conditions without exposing key material.
Execution infrastructure ensures that recovery actions follow deterministic processes, maintaining reliability across environments.
From an integration perspective:
- Wallet provisioning
- Authentication
- Account control
- Execution
operate as a coordinated system.
Recovery policies are configured through dashboard.abstraxn.com and enforced at the account layer, with integration handled through a single SDK call. Recovery logic runs on the same infrastructure as the paymaster and bundler.
Applications define recovery behavior. Infrastructure enforces it.
Conclusion
Seed phrases were designed for ownership, not recovery.
As Web3 systems evolve, this limitation becomes more visible. Onboarding has improved. Execution has become programmable. Recovery remains underdeveloped.
Account recovery without seed phrase addresses this gap by shifting responsibility to system design.
Wallets are no longer static access points. They are continuous systems that must maintain access, enforce control, and handle failure predictably.
Onboarding is solved. Execution is solved. Recovery is the work that remains, and it is the work that determines which Web3 applications operate reliably at scale.